

Email Threat Review April 2021
Summary
In this second installment of our monthly email threat review, we present an overview of the email-based threats observed in April 2021 and compare it with March 2021.
The report provides insights into:
- Unwanted emails by category
- File types used in attacks
- Industry Email Threat Index
- Attack techniques
- Impersonated company brands and organizations
- Highlighted threat email campaigns
- Ransomleaks
Unwanted emails by category
The following table shows the distribution of unwanted emails by categories.
| Email category | % |
| Rejected | 78.60 |
| Spam | 16.41 |
| Threat | 4.05 |
| AdvThreat | 0.89 |
| Content | 0.04 |
The following time histogram shows the email volume per category per hour.

Unlike in March, there were no obvious anomalous spikes in the unwanted email volumes in April.
Methodology
The listed email categories correspond to the email categories listed in the Email Live Tracking of Hornetsecurity’s Control Panel. So our users are already familiar with them. For others, the categories are:
| Category | Description |
| Spam | These emails are unwanted and are often promotional or fraudulent. The emails are sent simultaneously to a large number of recipients. |
| Content | These emails have an invalid attachment. The administrators define in the Content Control module which attachments are invalid. |
| Threat | These emails contain harmful content, such as malicious attachments or links, or they are sent to commit crimes like phishing. |
| AdvThreat | Advanced Threat Protection has detected a threat in these emails. The emails are used for illegal purposes and involve sophisticated technical means that can only be fended off using advanced dynamic procedures. |
| Rejected | Our email server rejects these emails directly during the SMTP dialog because of external characteristics, such as the sender’s identity, and the emails are not analyzed further. |
File types used in attacks
The following table shows the distribution of file types used in attacks.
| File type (used in malicious emails) | % |
| Archive | 35.6 |
| Other | 17.6 |
| HTML | 17.3 |
| Excel | 7.6 |
| Executable | 7.0 |
| 4.8 | |
| Disk image files | 4.6 |
| Word | 3.5 |
| Powerpoint | 1.3 |
| Script file | 0.5 |
| 0.1 | |
| LNK file | 0.0 |
The following time histogram shows the email volume per file type used in attacks per 7 days.

Archives (.zip, .rar, .gzip, .ace, .tar.gz, etc.) are more popular. The most prevalent use for archives in attacks is compressing the malware executable and attaching it directly to the attack email. This is done in hopes that the targeted email system is not able to scan compressed attachments. Low-quality criminal threat actors often use this technique as it does not require any technical expertise. Another use for archives is to compress malicious documents. This is also done to reduce detection.
HTML files (.htm, .html, etc.) are used either for phishing, having the phishing website attached directly to the email1 (thus circumventing URL filters), redirecting victims to websites for malware downloads (again to not directly include a clickable URL in the email), or social engineering.
Excel files (.xls, .xlsm, .xlsx, .xslb, etc.) with their XLM macros gained popularity last year. Unlike VBA macros malware, XLM macro malware is less detected and thus favored by many threat actors.3,2 In fact, many threat actors use the same malicious document generator called “EtterSilent” to generate their XLM macro documents.
PDFs (.pdf) use embedded links or other social engineering lures.3
Attaching executables (.exe) directly to emails is the laziest approach. It is used mainly by low-quality criminal threat actors.
Disk image files (.iso, .img, etc.) are used similarly to archives.4 Windows can automatically mount disk image files similarly to ZIP files.
Industry Email Threat Index
The following table shows the Top 10 of our Industry Email Threat Index calculated based on the number of threat emails compared to clean emails received (in median) by each industry.
| Industries | Share of threat in threat and clean emails |
| Research industry | 5.0 |
| Manufacturing industry | 3.9 |
| Media industry | 3.6 |
| Hospitality industry | 3.6 |
| Education industry | 3.5 |
| Healthcare industry | 3.5 |
| Automotive industry | 3.3 |
| Transport industry | 3.2 |
| Retail industry | 3.0 |
| Information technology industry | 3.0 |
The following bar chart visualizes the email-based threat posed to each industry.
- March 2021:
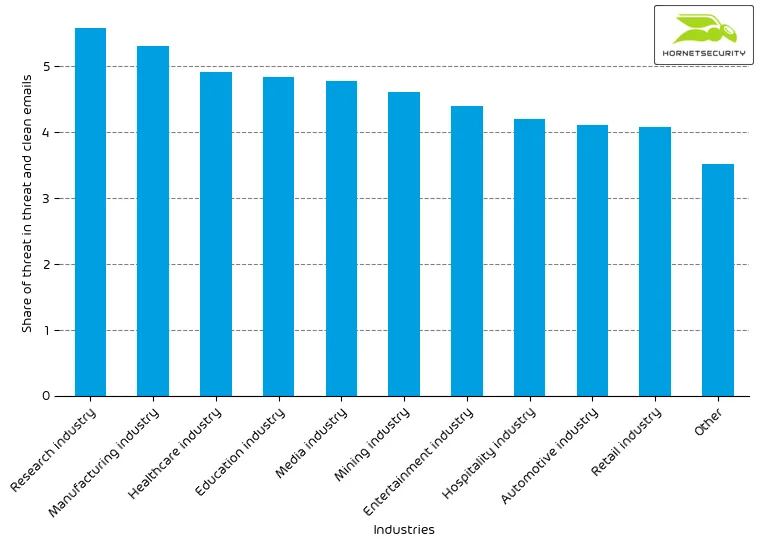
- April 2021:
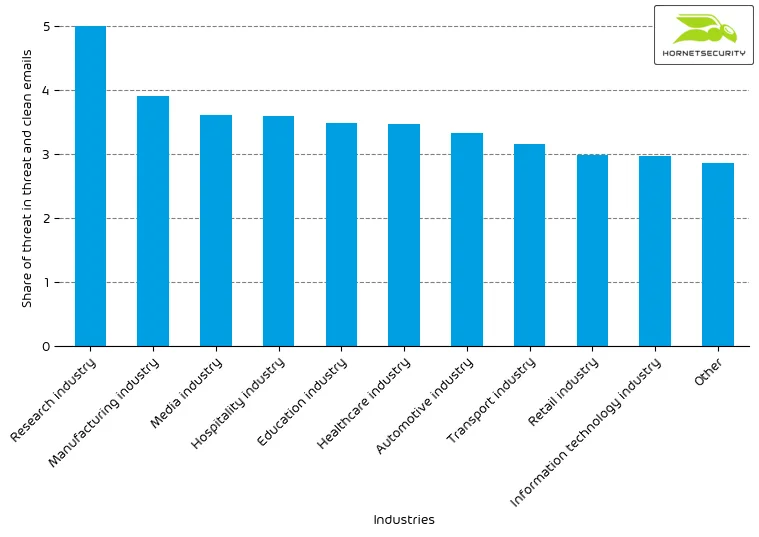
The global median of threat emails in threat and clean emails for organizations fell from 3.7% in March to 3.0% in April. This decrease can be seen for all industries. However, while the manufacturing industry dropped from 5.3% to 3.9% and the other industries similarity the research industry remains at 5% ratio of threat emails in their received threat and clean emails.
Methodology
Different (sized) organizations receive a different absolute number of emails. Thus, to compare organizations, we calculated the percent share of threat emails from each organization’s threat and clean emails. We then calculate the median of these percent values over all organizations within the same industry to form the industry’s final threat score.
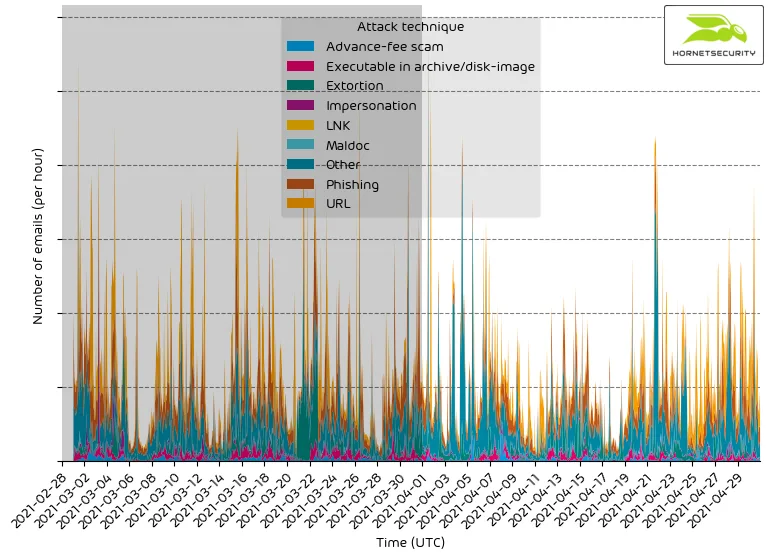
Attack techniques
The following table shows the attack technique used in attacks.
| Attack technique | % |
| Other | 38.4 |
| Phishing | 23.4 |
| URL | 20.8 |
| Extortion | 9.0 |
| Executable in archive/disk-image | 3.4 |
| Advance-fee scam | 2.8 |
| Impersonation | 1.8 |
| Maldoc | 0.4 |
| LNK | 0.0 |
The following time histogram shows the email volume per attack technique used per hour.
Impersonated company brands and organizations
The following table shows which company brands our systems detected most in impersonation attacks.
| Impersonated brand or organization | % |
| Amazon | 23.0 |
| DocuSign | 21.5 |
| Deutsche Post / DHL | 11.9 |
| PayPal | 3.4 |
| Microsoft | 2.9 |
| 2.8 | |
| 1&1 | 2.6 |
| HSBC | 2.2 |
| Unicredit | 1.6 |
| O2 | 1.5 |
| Others | Rest |
The following time histogram shows the email volume for company brands detected in impersonation attacks per hour.
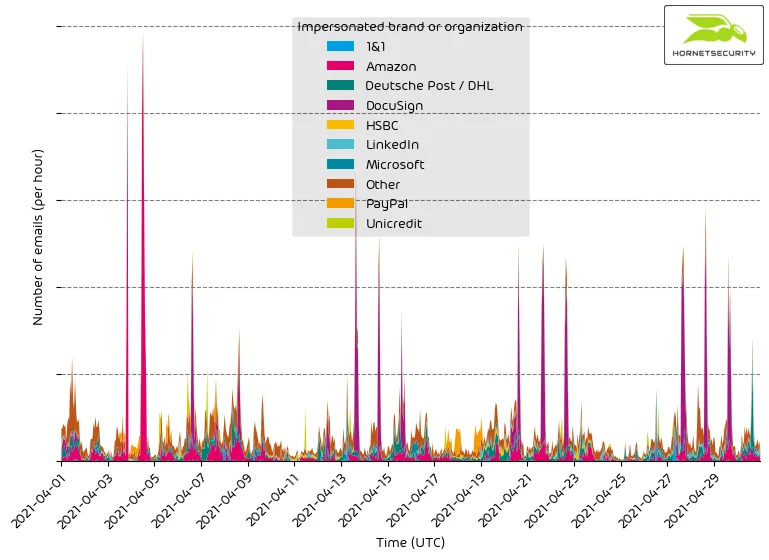
It’s a constant stream of phishing and other attacks impersonating big brands to entice recipients to open the emails.
A reoccurring Hancitor malspam campaign dominates the impersonation of the DocuSign brand.
Highlighted threat email campaigns
In this section, we want to highlight some malspam campaigns of prominent, well-known threat actors.
The following time histogram shows the email volume per hour for a list of highlighted threat email campaigns.
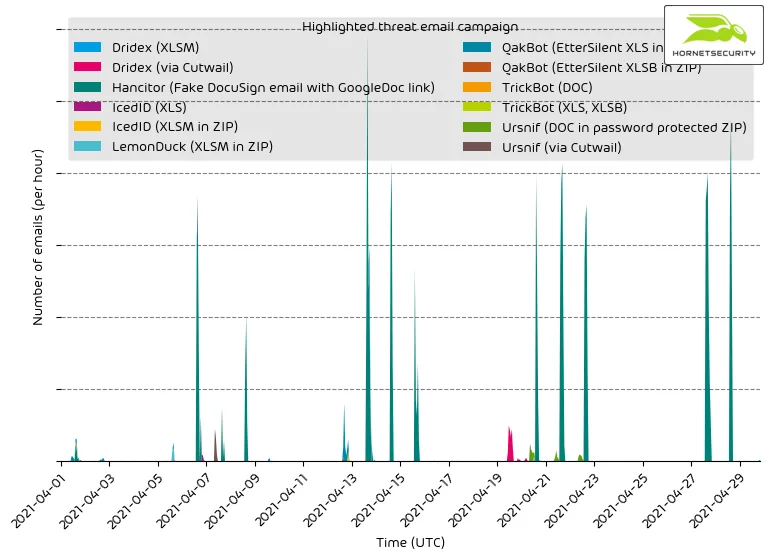
Please be advised that this does not contain all campaigns. The ranking, as well as volume figures, should therefore not be taken as a global ranking. We strive to expand this section of our reporting in the future.
We can see that the malspam waves of the selected campaigns have well-defined start and endpoints, unlike less sophisticated mass-spam email campaigns, which will send email in a constant stream.
As outlined earlier in the section on impersonated company brands or organizations the reoccurring Hancitor malspam campaign pretends to be documents send via DocuSign. The campaign spikes correspond to the previously spikes in DocuSign impersonation detections.
One shown campaign stands out not because of its volume but for its low detection rate by other security solutions. The Cutwail-A botnet updated their XLSM maldocs. This time it was distributing Ursnif.
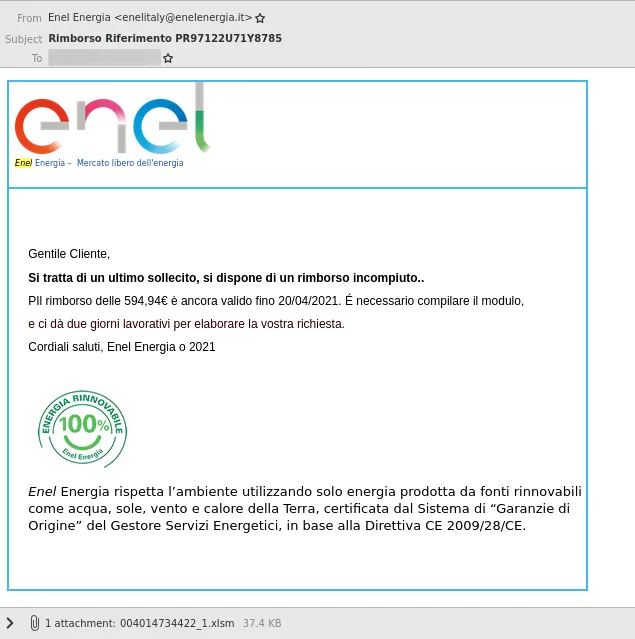
At the time of delivery, the maldocs of the campaign were detected by only 3 of 62 detections on VirusTotal.
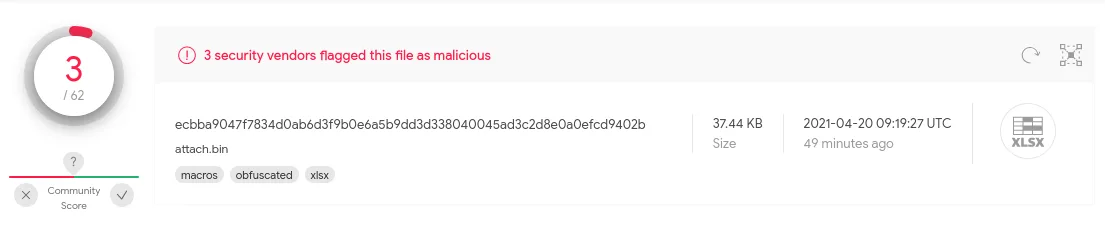
We are aware that VirusTotal detection does not represent the real dynamic detection of the listed security products. However, because the campaign was already caught by Hornetsecurity’s Spam and Malware filter using static detection signatures, it is an apples-to-apples comparison and outlines Hornetsecurity’s detection capabilities when it comes to threat email detection.
Methodology
Hornetsecurity observes hundreds and thousands of different threat email campaigns of varying threat actors ranging from very unsophisticated low-effort attacks to highly complex obfuscated attack schemes. Our highlighting includes only major sophisticated threat email campaigns.
Ransomleaks
Threat actors continue to leak data stolen from ransomware victims to pressure them into paying not only for decrypting the files encrypted by the ransomware but also for not making the data stolen before encryption public. We observed the following number of leaks on ransomware leaksites:
| Leaksite | Number of victim data leaks |
| Conti | 41 |
| Avaddon | 40 |
| REvil | 33 |
| Darkside | 19 |
| Babuk | 17 |
| Ragnarok | 12 |
| Astro Team | 10 |
| Cl0p | 9 |
| Everest | 5 |
| RansomEXX | 2 |
| Nephilim | 1 |
| RagnarLocker | 1 |
The following bar chart visualizes the number of victim data leaks per leaksite.
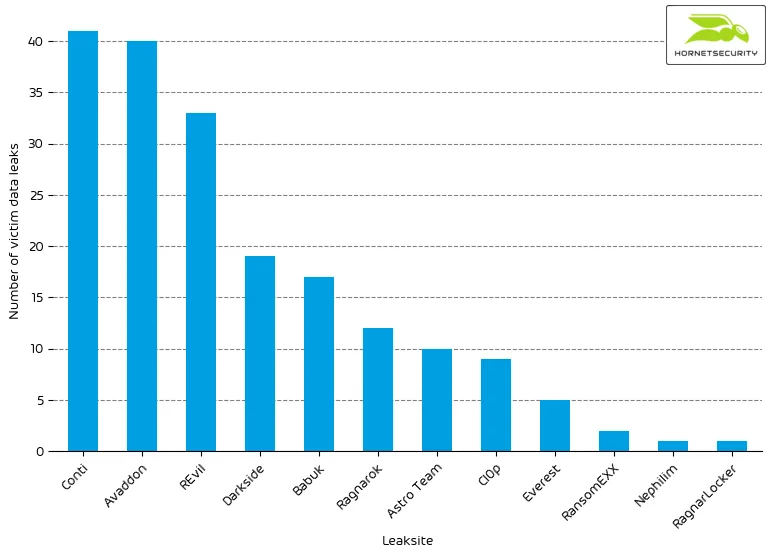
This month the Darkside ransomware group announced that they offer insider trading information for sale. Short sellers could buy information on companies compromised by Darkside ransomware before publication on the Darkside leaksite.
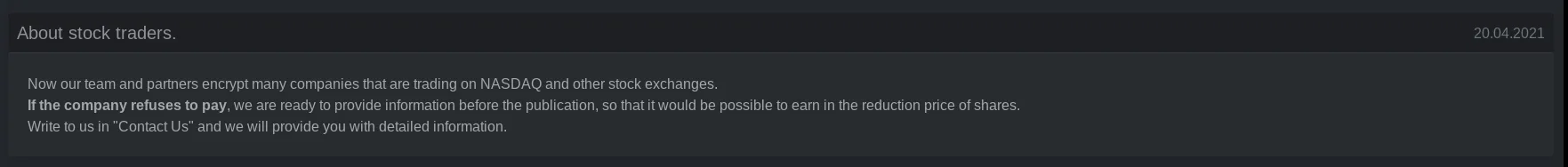
After the announcement, Darkside started tagging their posted victims with their respective stock tickers.
Also, this month the Babuk ransomware announced the closing of their ransomware operation.
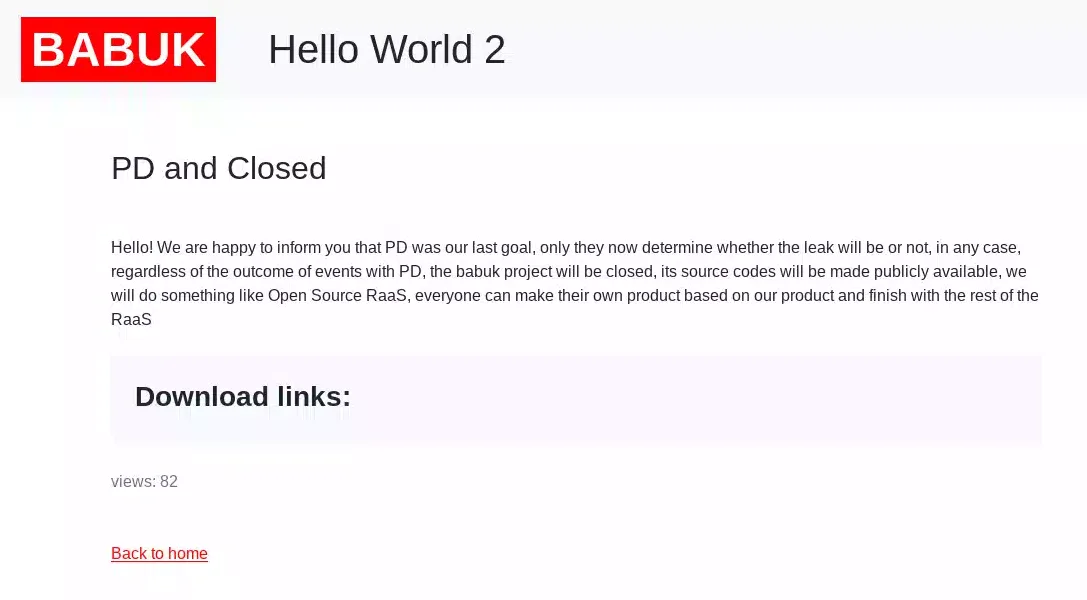
However, only a few days later, they clarified that they would only close the ransomware part of their operation. They will continue stealing data from victims and extorting them with the publication of the stolen data.
Conclusion
We hope you found the second installment of our monthly email threat review informative. Get back next month for more and updated email threat landscape insights.
References
- 1 https://www.hornetsecurity.com/en/security-informationen-en/html-phishing-asking-for-the-password-twice/
- 2 https://www.hornetsecurity.com/en/threat-research/qakbot-distributed-by-xlsb-files/
- 3 https://www.hornetsecurity.com/en/threat-research/bazarloaders-elaborate-flower-shop-lure/
- 4 https://www.hornetsecurity.com/en/security-information/information-stealer-campaign-targeting-german-hr-contacts/


